Industrial manufacturer Siemens is encouraging users running devices that use its Ruggedcom Discovery Protocol (RCDP) to apply firmware updates this week. The updates resolve a serious and remotely exploitable vulnerability that could let an attacker carry out administrative actions.
The issue, an improper access control vulnerability, could allow users of networks adjacent to targeted devices to perform unauthorized administrative actions, according to an advisory made public by ICS-CERT, the Industrial Control Systems Cyber Emergency Response Team, on Thursday.
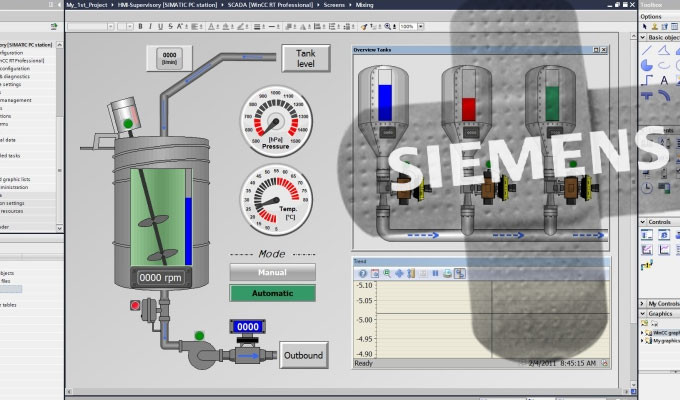
Technically the vulnerability, which rates as an 8.8 on the CVSS v3.0 system, allows users to write to the device, something which shouldn’t be possible. The vulnerability affects devices such as RUGGEDCOM switches and serial-to-ethernet devices, along with SCALANCE X switches. The devices are usually found in electric utility substations and can often be used to connect programmable logic controllers (PLCs) or human machine interfaces (HMIs).
Specifically the issue affects the following devices that use Ruggedcom:
RUGGEDCOM ROS for RSL910 devices: All versions prior to ROS v5.0.1
RUGGEDCOM ROS for all other devices: All versions prior to ROS v4.3.4
SCALANCE XB-200/XC-200/XP-200/XR300-WG: All versions newer than v3.0
SCALANCE XR-500/XM-400: All versions newer than v6.1
Siemens pushed out updates for products running Ruggedcom ROS this week but is still readying updates for Scalance devices. Users running Ruggedcom ROS can update to versions 4.3.4, 5.0.1, and Explorer 1.5.2 to fix the vulnerability free of charge.
While Siemens claims there are no public exploits known to target the vulnerability, the German conglomerate is still encouraging users running Scalance devices to manually deactivate RCDP to mitigate the vulnerability.
Source: https://threatpost.com/siemens-patches-improper-access-vulnerability-in-ruggedcom-protocol/128214/




